Security isn’t just about building walls; it’s about building trust.
That’s why we’ve taken a leap towards transparency by making Otterize open source.
We believe in security for all
Transparency, innovation, and trust are at the core of our mission. Join us in shaping a safer digital future, together. Explore, contribute, and strengthen security with Otterize.
Transparency builds trust
See the code, trust the code. Our open source approach ensures transparency and accountability.
Constant evolution
Security never stands still. By going open source, Otterize stays on the cutting edge of protection. Join us in shaping the future of security.
Community-powered innovation
Collaboration fuels innovation. With open source, we invite you to join our community and share ideas, and build a secure digital world together.
What are you waiting for? Experience the power of Otterize OSS for yourself
Simplify network policy management
Why make things complicated when they can be simple? At Otterize, we’re all about making your life easier.
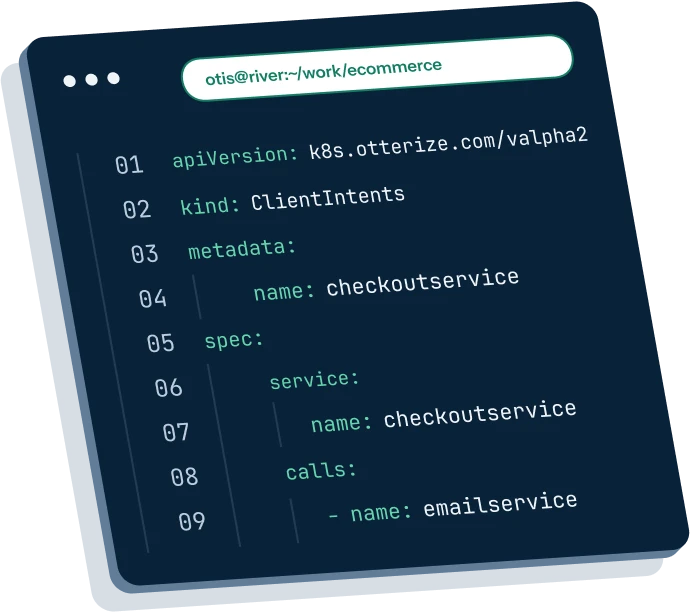
Client intents: your new best friend
Forget the hassle of managing pod identities and labels or diving deep into network policy configurations. Say hello to client intents—the easy way to set access controls.
Bootstrap with ease
Starting from scratch? No worries! Bootstrap client intents effortlessly by using network mapper to learn from existing traffic patterns.
- Kubernetes
Scheduler vs. API Proxy: Balancing Kubernetes data-plane and control-plane for optimal Zero-Trust IAM security with Otterize
Discover how to automate zero-trust IAM security for EKS applications and AWS resources using AWS Controllers for Kubernetes (ACK) and Otterize.
- Kubernetes
First Person Platform Episode 2 - Andrew Moore on Uber Workload Identity and Authorization
The second episode of First Person Platform, a podcast: platform engineers nerd out with Ori Shoshan on access controls, Kubernetes, and platform engineering.
- Network Policy
Network policies are not the right abstraction (for developers)
We explore the limitations of relying solely on Kubernetes network policies as a solution for achieving zero-trust between pods, identifying multiple flaws that hinder their effectiveness in meeting the demands of real-world use cases, particularly when prioritizing developer experience in a Kubernetes-based platform.